Introduction
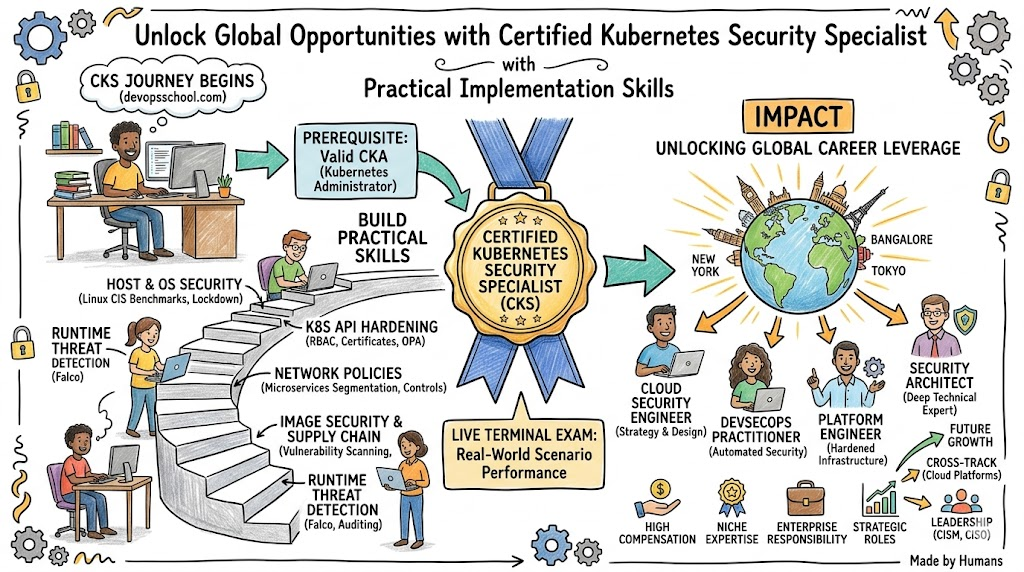
Engineers today face a landscape where container vulnerabilities represent a primary threat to business continuity. Mastering the Certified Kubernetes Security Specialist (CKS) Certification empowers you to transform from a standard administrator into a specialized guardian of cloud-native assets. This roadmap provides the clarity required to navigate high-stakes security configurations and performance-based assessments. If you seek to lead in this domain, DevOpsSchool delivers the hands-on expertise necessary to dominate the command line and secure your production environments against sophisticated attackers.
What is the Certified Kubernetes Security Specialist (CKS) Certification Training Course?
The Certified Kubernetes Security Specialist (CKS) Certification Training Course acts as a professional crucible for those who must protect sensitive workloads. It moves beyond basic setup and configuration, focusing instead on the proactive defense of the entire container lifecycle. You learn to intercept threats during the build phase, enforce strict policies during deployment, and monitor for anomalies during runtime.
This program bridges the gap between infrastructure management and professional cybersecurity. It forces practitioners to adopt a “zero-trust” mentality within the cluster, treating every component as a potential vector for compromise. By completing this training, you demonstrate that you can manage the complex security surface of a modern, multi-tenant Kubernetes platform effectively.
Who Should Pursue Certified Kubernetes Security Specialist (CKS) Certification Training Course?
Senior DevOps professionals and Site Reliability Engineers (SREs) who oversee mission-critical clusters find this certification vital for their daily operations. Security engineers who need to translate traditional network defense into the world of pods and services also benefit immensely from this technical deep dive. In India’s booming tech sector and the global market, hiring managers look for this specific credential to identify engineers capable of handling sensitive financial or healthcare data.
Technical leads and architects should also pursue this track to ensure they design systems with security as a foundational element rather than a post-launch addition. While it targets those with significant experience, it provides a clear benchmark for any cloud professional aiming to reach the pinnacle of the platform engineering field.
Why Certified Kubernetes Security Specialist (CKS) Certification Training Course is Valuable
The value of this certification lies in its direct impact on organizational risk reduction. As data breaches become more frequent and costly, specialists who can harden clusters provide an immediate return on investment for their employers. Earning the CKS badge proves you possess the technical stamina and precision required to work in high-pressure, live environments where mistakes have real-world consequences.
Furthermore, this certification ensures long-term career resilience. While individual security tools may come and go, the core principles of identity management, supply chain security, and system auditing remain constant. You gain a prestigious credential that commands respect in the industry and opens doors to elite consulting and leadership opportunities.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Overview
DevOpsSchool delivers the training for this program through the Certified Kubernetes Security Specialist (CKS) Certification Training Course link provided above. The exam itself utilizes a performance-based format, meaning you must solve real-world security puzzles in a live terminal rather than answering multiple-choice questions. This structure ensures that every certified professional can actually execute the tasks they claim to master.
The Cloud Native Computing Foundation (CNCF) maintains the curriculum to reflect the most current threats and defensive strategies. You have two hours to navigate several clusters, fixing misconfigured API servers, implementing network policies, and auditing system logs. This rigorous approach maintains the high prestige of the certification and guarantees its relevance in a fast-paced technology market.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Tracks & Levels
The journey to specialist status involves a logical progression through cloud-native administration and security. You start at the foundational level by learning the basics of containerization and orchestration. You then move to the associate level, which requires you to pass the Certified Kubernetes Administrator (CKA) exam—a mandatory prerequisite for the CKS.
Advanced tracks allow you to specialize further in areas like DevSecOps or SRE-focused security. Each level builds upon the last, ensuring you have a comprehensive understanding of how to build and manage a cluster before you attempt to secure it. This tiered approach prevents knowledge gaps and ensures that CKS holders are well-rounded engineers capable of handling any infrastructure challenge.
Complete Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Cloud-Native | Foundational | Career Starters | None | Docker, Cloud Basics | 1 |
| Admin | Associate | DevOps Engineers | Foundational Skills | Cluster Ops, Networking | 2 |
| Security | Professional | Senior Engineers | Active CKA | Hardening, Compliance | 3 |
| Architecture | Advanced | Tech Leads | CKS + CKA | Multi-cluster Security | 4 |
Detailed Guide for Each Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification
Foundational Level
The foundational level introduces you to the essential concepts of modern cloud infrastructure. You explore the role of containers in software delivery and learn why security must be a priority from the very first line of code. This stage provides the context you need to understand why Kubernetes requires specialized defensive measures.
Associate Level
The Associate level focuses on the CKA (Certified Kubernetes Administrator) domain. You learn to install clusters, manage storage, and troubleshoot networking. This stage is critical because you cannot effectively secure a system unless you fundamentally understand how it operates and how its components interact under normal conditions.
Professional/Specialty Level
The Professional level centers on the CKS exam and its core security domains. You transition from a “builder” to a “defender,” focusing on limiting privileges and closing vulnerabilities. This level requires you to master third-party tools that extend the native security capabilities of Kubernetes to protect against advanced persistent threats.
Certified Kubernetes Security Specialist (CKS) Certification Training Course – CKS Professional
What it is
The CKS validates your technical ability to secure container-based applications across the entire lifecycle. You prove that you can harden the control plane, protect the worker nodes, and ensure the integrity of every container running in your environment.
Who should take it
Experienced administrators who bear the responsibility of maintaining production-grade Kubernetes environments should take this exam. It is the definitive credential for DevOps and security specialists who want to showcase their elite technical skills.
Skills you’ll gain
- You configure the API server and Kubelet with the most secure settings.
- You use Admission Controllers to prevent unauthorized deployments.
- You implement Network Policies to restrict pod-to-pod communication.
- You scan images for vulnerabilities and sign them to ensure authenticity.
- You monitor system calls and runtime activity to detect active breaches.
Real-world projects you should be able to do
- You audit a legacy Kubernetes cluster and bring it up to CIS benchmark standards.
- You build an automated pipeline that blocks containers with critical CVEs.
- You set up a zero-trust network environment for sensitive financial applications.
- You configure an automated runtime alerting system that flags unauthorized file access.
Preparation plan
- 7–14 days: You master the Kubernetes documentation and review the core CKA concepts to ensure your administrative speed is at its peak.
- 30 days: You dive deep into tools like Falco, Kube-bench, and Trivy, practicing their installation and configuration in a lab environment.
- 60 days: You run through simulated exams repeatedly, focusing on accuracy in the terminal and managing the two-hour time limit effectively.
Common mistakes
- Many candidates underestimate the time pressure of the live exam and fail to move past difficult questions quickly.
- Engineers often forget to check the specific documentation for third-party tools allowed during the test.
- Failing to practice the CKA prerequisite material leads to basic administrative errors that waste valuable exam time.
Best next certification after this
- Same-track option: Advanced Cloud Security Specialist.
- Cross-track option: Certified Kubernetes Application Developer (CKAD).
- Leadership option: Certified Information Systems Security Professional (CISSP).
Choose Your Learning Path
DevOps Path
The DevOps path focuses on the seamless integration of security into the development pipeline. You learn to create automated guardrails that allow developers to ship code quickly without bypassing security protocols. This path emphasizes the “Shift Left” philosophy, identifying risks long before they reach the production environment.
DevSecOps Path
The DevSecOps path places security at the center of the engineering culture. You specialize in vulnerability management, compliance-as-code, and securing the software supply chain. Professionals on this path act as the bridge between technical security teams and the operational DevOps squads.
SRE Path
The SRE path views security through the lens of system reliability. You focus on building resilient clusters that can withstand attacks without suffering downtime. This path involves mastering monitoring tools and incident response procedures to ensure that security events do not impact the availability of the platform.
AIOps Path
The AIOps path explores the intersection of artificial intelligence and infrastructure management. You use machine learning to analyze security logs and detect patterns that traditional monitoring might miss. This path is ideal for those who want to use automated intelligence to defend large-scale, complex environments.
MLOps Path
The MLOps path secures the specialized infrastructure used for machine learning. You focus on protecting data pipelines and securing model artifacts from unauthorized access. This path ensures that the intellectual property of the organization remains safe while running on Kubernetes.
DataOps Path
The DataOps path prioritizes the security of data processing and storage. You learn to protect persistent volumes and ensure that data remains encrypted at every stage of its journey through the cluster. This path is essential for engineers working in data-sensitive industries like finance or healthcare.
FinOps Path
The FinOps path connects technical security measures with financial efficiency. You ensure that security tools and configurations do not lead to unnecessary cloud costs. This path requires a deep understanding of how security decisions impact the overall budget of the infrastructure.
Role → Recommended Certified Kubernetes Security Specialist (CKS) Certification Training Course Certifications
| Role | Recommended Certifications |
| DevOps Engineer | CKA, CKS, CKAD |
| SRE | CKA, CKS, Prometheus Monitoring |
| Platform Engineer | CKA, CKS, AWS Solutions Architect |
| Cloud Engineer | CKA, CKS, Terraform Associate |
| Security Engineer | CKS, CompTIA Security+, OSCP |
| Data Engineer | CKA, CKS, Data Governance Cert |
| FinOps Practitioner | CKS, FinOps Certified Practitioner |
| Engineering Manager | CKS, PMP, ITIL |
Next Certifications to Take After Certified Kubernetes Security Specialist (CKS) Certification Training Course
Same Track Progression
Deep specialization within the security track involves exploring advanced networking or service mesh security. These certifications allow you to master the granular details of how microservices communicate and how to implement mutual TLS across a large organization. You become the go-to expert for high-complexity, high-security cloud environments.
Cross-Track Expansion
Skill broadening might involve pursuing the CKAD (Certified Kubernetes Application Developer) to understand the developer’s perspective better. You can also target professional-level certifications from cloud providers like Azure or AWS. This versatility makes you a more valuable asset as you can secure Kubernetes across any cloud ecosystem.
Leadership & Management Track
If you aim for leadership, the next step involves management-focused certifications that bridge the gap between technical work and business strategy. You learn to manage budgets, lead security teams, and communicate risk to non-technical stakeholders. This transition allows you to influence the security posture of an entire company.
Training & Certification Support Providers for Certified Kubernetes Security Specialist (CKS) Certification Training Course
- DevOpsSchool offers an immersive learning experience that prioritizes hands-on lab work and real-world scenarios. Their instructors guide you through the complexities of the CKS curriculum, ensuring you can handle the pressure of the performance-based exam. They provide a structured path that takes you from the basics of administration to the heights of security expertise.
- Cotocus provides high-end consulting and training for enterprise teams looking to secure their containerized workloads. Their bootcamps focus on deep technical hardening and the practical application of security tools in production. They help engineers build the technical intuition needed to identify and fix vulnerabilities before attackers can exploit them.
- Scmgalaxy serves as a massive community hub where you can find tutorials, study guides, and practice tests for the CKS. Their resources are designed for self-paced learners who want to supplement their training with community knowledge. They offer a wide variety of scenarios that help you prepare for the unpredictable nature of the live exam.
- BestDevOps specializes in exam preparation that focuses on speed and accuracy in the terminal. Their CKS course breaks down the most difficult domains into manageable lessons, helping you build confidence in your command-line skills. They provide expert tips on how to navigate the exam environment effectively to maximize your score.
- devsecopsschool.com focuses exclusively on the integration of security into the DevOps lifecycle. Their training programs teach you how to automate security policies and protect the entire software supply chain. This provider is ideal for engineers who want to become leaders in the DevSecOps movement within their organizations.
- sreschool.com approaches Kubernetes security from the perspective of platform reliability. Their courses emphasize the importance of monitoring and incident response in maintaining a secure and stable environment. They prepare you to handle the operational challenges of securing large-scale, distributed systems without sacrificing uptime.
- aiopsschool.com teaches you how to leverage artificial intelligence to enhance your security operations. You learn to use AI-driven tools to analyze logs and detect threats in real-time, providing an extra layer of defense for your clusters. This forward-looking provider is perfect for engineers interested in the future of automated security.
- dataopsschool.com focuses on the unique security needs of data-heavy workloads on Kubernetes. Their training covers everything from securing data pipelines to protecting persistent storage volumes. They ensure you have the skills to keep sensitive information safe while it is being processed and stored in the cloud.
- finopsschool.com bridges the gap between technical security and cloud cost management. Their courses help you understand how to implement a secure architecture that is also cost-effective. This provider is essential for senior engineers who need to balance the security needs of the platform with the organization’s budget.
Frequently Asked Questions (General)
1. Is the CKS exam more difficult than the CKA?
Most professionals consider the CKS much harder because it adds a deep layer of security tools and complex configurations on top of standard administration.
2. How long must I wait to retake the exam if I fail?
The Linux Foundation typically allows you to schedule your free retake within a few days, though you should spend time reviewing your weak areas first.
3. Can I use a personal laptop for the proctored exam?
You can use a personal machine as long as it meets the hardware and software requirements, including a working webcam and a stable internet connection.
4. Do I need to be a security expert before starting this course?
You don’t need to be an expert, but a strong foundation in Kubernetes administration and basic Linux security concepts is highly recommended.
5. Are the labs provided by training sites similar to the real exam?
Top-tier training providers design their labs to mimic the exam environment’s interface and difficulty to prepare you for the actual test.
6. What version of Kubernetes does the exam currently use?
The exam tracks the most recent stable releases, usually updating within one or two minor versions of the current Kubernetes release.
7. Is the CKS certification recognized globally?
Yes, the CKS is globally recognized as the gold standard for Kubernetes security and is highly valued by major tech companies worldwide.
8. Can I take the CKS exam without the CKA prerequisite?
No, you must have a valid CKA certification on your record to be eligible to receive the CKS certification upon passing the exam.
9. How much does the CKS exam cost?
The exam price varies but typically sits around $395 USD, though you can often find discounts through training providers like DevOpsSchool.
10. What documentation can I access during the exam?
You are permitted to access official Kubernetes documentation and certain third-party tool sites specifically mentioned in the exam rules.
11. Is there a time limit for the CKS exam?
You have exactly two hours to complete all the tasks in the performance-based exam, making time management a critical skill.
12. How often do I need to renew my CKS certification?
The CKS certification remains valid for two years, after which you must retake the exam to maintain your specialist status.
FAQs on Certified Kubernetes Security Specialist (CKS) Certification Training Course
1. Does the course cover image scanning with Trivy?
Yes, the curriculum includes hands-on practice with scanning tools like Trivy to identify and remediate vulnerabilities in your container images.
2. Will I learn how to use AppArmor and Seccomp?
You will master the implementation of AppArmor profiles and Seccomp filters to restrict the system calls containers can make to the host kernel.
3. Is Admission Controller configuration part of the training?
The course provides detailed lessons on configuring various admission controllers to enforce security policies and prevent insecure deployments.
4. Does the training include runtime security with Falco?
You will learn how to install Falco and write custom rules to detect suspicious activities like shell execution inside a running container.
5. Will I learn how to secure the ETCD database?
The training covers the essential steps for securing the ETCD cluster, including encryption at rest and restricting access to the database.
6. Does the course teach me how to manage Secrets securely?
You will learn best practices for Secrets management, including encryption providers and avoiding the storage of sensitive data in plain text.
7. Is auditing and logging covered in the CKS curriculum?
The course teaches you how to configure Kubernetes auditing to track who did what and when, which is vital for post-incident analysis.
8. Will I learn how to harden the host operating system?
You will explore strategies for securing the underlying nodes, including minimizing installed software and restricting SSH access to the workers.
Final Thoughts: Is Certified Kubernetes Security Specialist (CKS) Certification Training Course Worth It?
Taking the leap into the Certified Kubernetes Security Specialist (CKS) Certification Training Course marks a significant milestone in your professional development. As organizations shift their most valuable data to the cloud, the need for individuals who can protect that data has never been higher. This certification doesn’t just teach you how to use tools; it changes the way you think about infrastructure, forcing you to prioritize safety and resilience in every decision you make. While the path to certification is rigorous and demands a high level of technical discipline, the rewards are equally substantial. You join an elite group of professionals capable of defending complex systems against modern threats. For any engineer aiming to secure their future in the cloud-native ecosystem, the CKS is an indispensable asset that pays dividends for years to come.
Leave a Reply